Imagine this: Your bank sends you an email asking you to update your account details right away. The email has a recognizable tone and the bank’s logo, making it seem authentic. However, there’s a catch: this email is a well-crafted phishing scam aiming to fool you into divulging private information that could jeopardize your financial security.
Social engineering, a dangerous skill that involves manipulating people’s minds to obtain private information, poses a constant threat in the digital age. This strategy often leads to disastrous outcomes by exploiting our inherent trust and willingness to help.
But is social engineering illegal? The answer may not be straightforward, but it encompasses more than just a simple “yes or no.” Join me as we delve into the legality, expressions, and prevention strategies of immoral conduct.
What is social engineering?
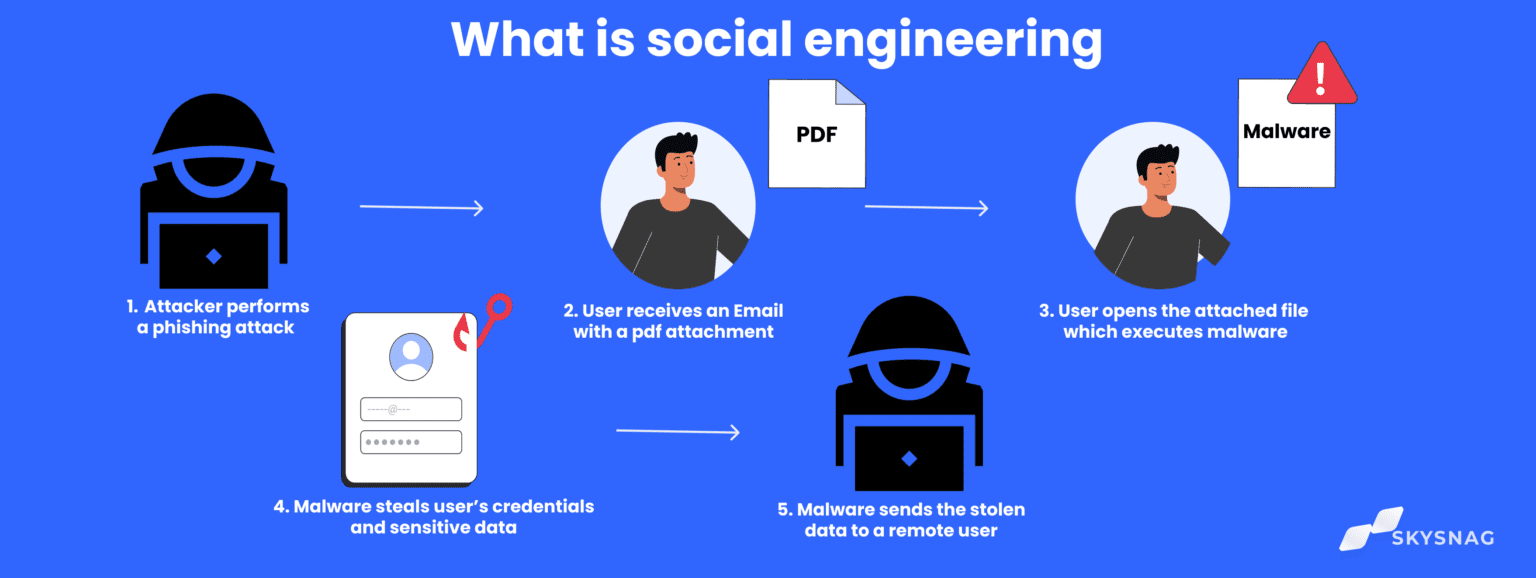
Social engineering is a technique that exploits human weaknesses to gain sensitive data or systems. It thrives on people’s innate capacity for cooperation and trust. Attackers use various strategies, including baiting, pretexting, and phishing emails, to trick victims into disclosing passwords, bank account information, or access credentials.
The legality of social engineering
Depending on the attacker’s intent and specific circumstances, social engineering may or may not be considered illegal. Social engineering is generally considered illegal when it aims to obtain private information or cause financial harm. Several laws and regulations cover social engineering activities, including:
- Computer Fraud and Abuse Act (CFAA): The Computer Fraud and Abuse Act (CFAA) prohibits using fraudulent methods to collect information or gain unauthorized access to computer systems.
- Identity Theft and Assumption Deterrence Act: The Identity Theft and Assumption Deterrence Act guards against the improper use of private data for commercial advantage.
- The Electronic Communications Privacy Act (ECPA) prohibits improper authorization for the interception of electronic communications.
Types of social engineering attacks
There are several types of social engineering attacks, each aiming to exploit particular flaws in individuals. Some frequent types of examples are:
- Phishing is the practice of sending false emails or text messages that look to be from genuine sources, such as banks or credit card firms, to fool victims into disclosing important information.
- Baiting: Attackers leave appealing goods in public locations, such as USB drives or infected software, to entice victims into installing malware or visiting malicious websites.
- Pretexting: Attackers create phony scenarios or mimic trustworthy individuals to earn victims’ trust and get access to sensitive information or systems.
Protecting yourself from social engineering
Social engineering attacks are complex, but individuals and organizations can take various precautions to protect themselves and their systems.
- Avoid answering unwanted calls, emails, or messages by being wary about clicking on links or opening attachments from senders you don’t know. Through a reliable method, contact the sender directly to confirm the legitimacy of requests.
- Make sure you enable multi-factor authentication and use strong passwords. For every account you have, create a strong, one-of-a-kind password. You should also enable multi-factor authentication, which provides an additional security layer on top of password security.
- Keep an eye out for your personal data. Steer clear of sending private information over unprotected channels, including passwords, social security numbers, and financial information.
- Report suspicious activity: Notify the relevant authorities of any strange emails, messages, or phone calls you receive.
Why is social engineering illegal?

Social engineering is a form of deception that can cause harm to individuals and organizations, making it illegal. Social engineers are breaking the law when they coerce someone into disclosing private information or taking actions that jeopardize their security. By exploiting human psychology and manipulating individuals into revealing sensitive information or granting unauthorized access, social engineering can lead to identity theft, financial loss, and even damage to national security.
It is illegal because it violates privacy rights, breaches trust, and facilitates criminal activities such as fraud and cybercrime. Laws are in place to protect individuals and organizations from the detrimental consequences of social engineering attacks.
Is social engineering a cyber crime?

Social engineering is a type of cybercrime. Social engineering is a type of cybercrime that involves obtaining illegal access to computer systems, networks, or personal information through human interaction and psychological manipulation.
Is social engineering harmful?
Yes, social engineering can be extremely dangerous. It can steal money, identities, and other critical information. It can also impair key infrastructure, harm reputations, and cause psychological discomfort.
Is blackmailing social engineering?
Social engineering also includes blackmail. Blackmailers use threats to expose humiliating or damaging information about someone unless their demands are met.
Why do hackers use social engineering?
Hackers use social engineering because it efficiently grants them access to information and systems. It is frequently easier to fool someone into exposing their password than brute-force it.
Is bribery social engineering?
Bribery is not usually considered a type of social engineering. When combined with social engineering, bribery enables the acquisition of access to information or systems.
What are the disadvantages of social engineering?
Social engineering has a number of disadvantages, including:
- Increased risk of cyber attacks: Organizations might become more exposed to cyber attacks due to social engineering.
- Damage to reputation: Social engineering attacks can harm an organization’s reputation.
- Loss of sensitive information: Social engineering attacks can result in the loss of sensitive data.
- Financial losses might result from social engineering attacks.
Who is behind social engineering?
A variety of people and organizations can perform social engineering attacks, including:
- Cybercriminals use social engineering to steal money, identities, and other sensitive information.
- Nation-states: Nation-states utilize social engineering to spy on and steal secrets from other countries.
- Hacktivists: Hacktivists disrupt operations and harm reputations by using social engineering.
- Insiders: Insiders utilize social engineering to get access to information and systems that they should not have access to.
Social engineering, a powerful cybercrime tool, raises ethical and legal issues, blurring boundaries and posing significant danger in the digital age. Victims of social engineering tactics can suffer severe consequences, including financial loss, identity theft, and reputational damage.
Vigilance and awareness are crucial tools against social engineering in the constantly evolving digital ecosystem. Educating ourselves, fostering a cybersecurity culture, and implementing robust protective measures can enhance our resilience and safeguard sensitive information from social engineering.
Maintain alertness and exercise caution to avoid social engineering attempts, as the power of deception is undeniable in the digital age.
Please share your knowledge and expertise with loved ones and coworkers to protect them from social engineering scams.
Leave a Reply